注意事项
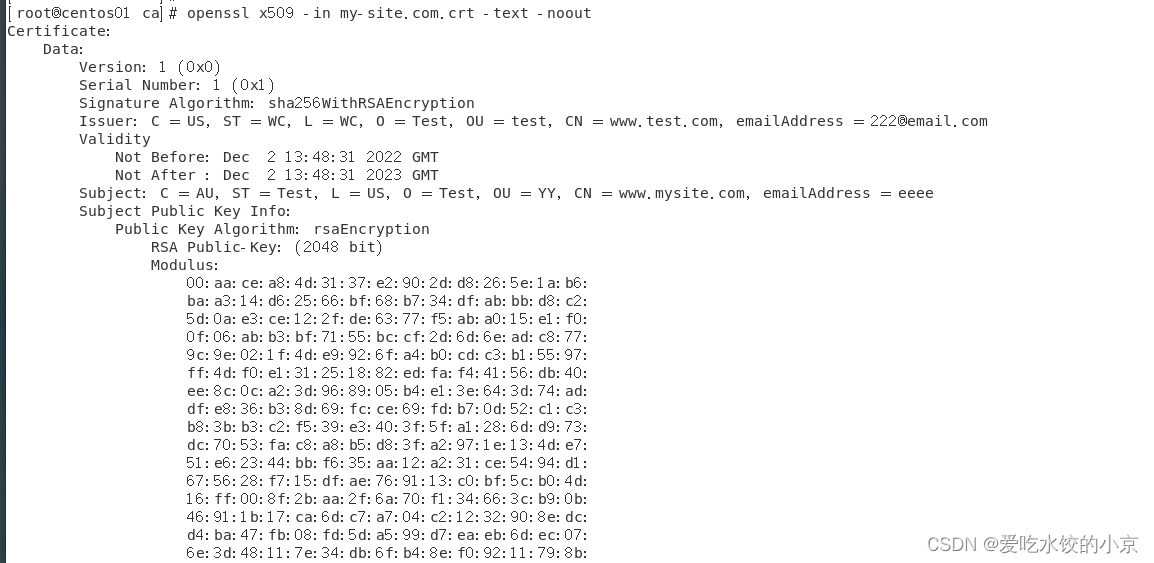
- 生成证书请求的填写 范例
- Subject: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = ca, emailAddress = ca@gmssl.com
- 前面的步骤存在错误,后面改用脚本进行证书生成,阅读时请跳过前面错误的内容
错误的内容 -> 开始
CA
- 生成私钥
- openssl ecparam -genkey -name SM2 -param_enc explicit -outform pem -out ca.key
- 生成请求
- openssl req -new -key ca.key -out ca.csr

- 生成自签名证书
- openssl x509 -req -days 365 -in ca.csr -signkey ca.key -out ca.crt
- 查看ca证书
- openssl x509 -text -in ca.crt
chy-cpabe@ubuntu:~/double_certificate/ca$ openssl x509 -text -in ca.crt
Certificate:Data:Version: 1 (0x0)Serial Number:13:d6:69:ae:15:ee:3e:c0:73:aa:67:d5:23:08:d5:45:51:77:9e:efSignature Algorithm: ecdsa-with-SHA256Issuer: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = ca, emailAddress = ca@gmssl.comValidityNot Before: Nov 28 05:55:02 2022 GMTNot After : Nov 28 05:55:02 2023 GMTSubject: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = ca, emailAddress = ca@gmssl.comSubject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:57:b3:c7:cd:72:ac:21:de:90:62:fd:9c:bf:06:42:68:5b:25:6c:ae:a6:e4:fb:1f:4a:95:27:b2:3a:1d:57:fd:e7:d4:4c:2b:c8:38:99:81:08:ec:77:f4:66:78:7f:17:e5:88:70:d7:aa:ac:f8:05:d1:22:da:18:43:7f:cf:12Field Type: prime-fieldPrime:00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:ffA: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:fcB: 28:e9:fa:9e:9d:9f:5e:34:4d:5a:9e:4b:cf:65:09:a7:f3:97:89:f5:15:ab:8f:92:dd:bc:bd:41:4d:94:0e:93Generator (uncompressed):04:32:c4:ae:2c:1f:19:81:19:5f:99:04:46:6a:39:c9:94:8f:e3:0b:bf:f2:66:0b:e1:71:5a:45:89:33:4c:74:c7:bc:37:36:a2:f4:f6:77:9c:59:bd:ce:e3:6b:69:21:53:d0:a9:87:7c:c6:2a:47:40:02:df:32:e5:21:39:f0:a0Order: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:72:03:df:6b:21:c6:05:2b:53:bb:f4:09:39:d5:41:23Cofactor: 1 (0x1)Signature Algorithm: ecdsa-with-SHA25630:44:02:20:34:10:62:ec:8b:34:ec:1b:dd:4d:fc:d7:d3:67:87:5b:1b:0b:5b:02:13:af:af:db:66:01:13:1a:d7:52:84:f3:02:20:35:6a:44:e0:f5:6e:d9:4d:be:2b:88:db:a4:61:d8:f3:45:38:40:8e:7f:65:93:7d:12:20:9b:66:0d:ec:61:87
-----BEGIN CERTIFICATE-----
MIICxDCCAmsCFBPWaa4V7j7Ac6pn1SMI1UVRd57vMAoGCCqGSM49BAMCMHcxCzAJ
BgNVBAYTAkNOMRAwDgYDVQQIDAdCZWlqaW5nMRAwDgYDVQQHDAdCZWlqaW5nMQww
CgYDVQQKDANNU0kxDDAKBgNVBAsMA21zaTELMAkGA1UEAwwCY2ExGzAZBgkqhkiG
9w0BCQEWDGNhQGdtc3NsLmNvbTAeFw0yMjExMjgwNTU1MDJaFw0yMzExMjgwNTU1
MDJaMHcxCzAJBgNVBAYTAkNOMRAwDgYDVQQIDAdCZWlqaW5nMRAwDgYDVQQHDAdC
ZWlqaW5nMQwwCgYDVQQKDANNU0kxDDAKBgNVBAsMA21zaTELMAkGA1UEAwwCY2Ex
GzAZBgkqhkiG9w0BCQEWDGNhQGdtc3NsLmNvbTCCATMwgewGByqGSM49AgEwgeAC
AQEwLAYHKoZIzj0BAQIhAP7/AAAAAP//
MEQEIP7/AAAAAP/8BCAo6fqenZ9eNE1a
nkvPZQmn85eJ9RWrj5LdvL1BTZQOkwRBBDLEriwfGYEZX5kERmo5yZSP4wu/8mYL
4XFaRYkzTHTHvDc2ovT2d5xZvc7ja2khU9Cph3zGKkdAAt8y5SE58KACIQD+
cgPfayHGBStTu/QJOdVBIwIBAQNCAARXs8fNcqwh3pBi/Zy/
BkJoWyVsrqbk+x9KlSeyOh1X/efUTCvIOJmBCOx39GZ4fxfliHDXqqz4BdEi2hhD
f88SMAoGCCqGSM49BAMCA0cAMEQCIDQQYuyLNOwb3U3819Nnh1sbC1sCE6+v22YB
ExrXUoTzAiA1akTg9W7ZTb4riNukYdjzRThAjn9lk30SIJtmDexhhw==
-----END CERTIFICATE-----
前情提要
- s -> 服务端
- c -> 客户端
- s -> 签名
- e -> 加密
- key -> 私钥
- pem -> 证书(格式的一种,此格式使用较为普遍)
服务端
签名
- 生成私钥
- openssl ecparam -genkey -name SM2 -param_enc explicit -outform pem -out ss.key
- 生成请求
- openssl req -new -key ss.key -out ss.csr

- 使用ca私钥进行签名,生成签名证书
- openssl x509 -req -days 365 -in ss.csr -signkey ../ca/ca.key -out ss.crt
chy-cpabe@ubuntu:~/double_certificate/first$ openssl x509 -text -in ss.crt
Certificate:Data:Version: 1 (0x0)Serial Number:59:9b:09:1b:a8:fc:b9:e7:a4:13:19:bb:15:bf:ea:40:dd:46:37:a5Signature Algorithm: ecdsa-with-SHA256Issuer: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = server_sign, emailAddress = server_sign@gmssl.comValidityNot Before: Nov 28 06:07:41 2022 GMTNot After : Nov 28 06:07:41 2023 GMTSubject: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = server_sign, emailAddress = server_sign@gmssl.comSubject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:57:b3:c7:cd:72:ac:21:de:90:62:fd:9c:bf:06:42:68:5b:25:6c:ae:a6:e4:fb:1f:4a:95:27:b2:3a:1d:57:fd:e7:d4:4c:2b:c8:38:99:81:08:ec:77:f4:66:78:7f:17:e5:88:70:d7:aa:ac:f8:05:d1:22:da:18:43:7f:cf:12Field Type: prime-fieldPrime:00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:ffA: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:fcB: 28:e9:fa:9e:9d:9f:5e:34:4d:5a:9e:4b:cf:65:09:a7:f3:97:89:f5:15:ab:8f:92:dd:bc:bd:41:4d:94:0e:93Generator (uncompressed):04:32:c4:ae:2c:1f:19:81:19:5f:99:04:46:6a:39:c9:94:8f:e3:0b:bf:f2:66:0b:e1:71:5a:45:89:33:4c:74:c7:bc:37:36:a2:f4:f6:77:9c:59:bd:ce:e3:6b:69:21:53:d0:a9:87:7c:c6:2a:47:40:02:df:32:e5:21:39:f0:a0Order: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:72:03:df:6b:21:c6:05:2b:53:bb:f4:09:39:d5:41:23Cofactor: 1 (0x1)Signature Algorithm: ecdsa-with-SHA25630:46:02:21:00:aa:aa:9a:3b:8e:76:5a:00:58:e2:62:96:f0:65:e4:31:3c:7f:16:54:99:31:e6:a1:25:53:9c:5c:03:eb:66:cd:02:21:00:fe:ce:ba:f0:a6:ec:df:9e:7a:72:87:a1:ca:ae:1f:7d:43:2c:a2:a7:e2:7e:0a:46:86:ca:81:e0:7c:17:c5:85
-----BEGIN CERTIFICATE-----
MIIC7DCCApECFFmbCRuo/LnnpBMZuxW/6kDdRjelMAoGCCqGSM49BAMCMIGJMQsw
CQYDVQQGEwJDTjEQMA4GA1UECAwHQmVpamluZzEQMA4GA1UEBwwHQmVpamluZzEM
MAoGA1UECgwDTVNJMQwwCgYDVQQLDANtc2kxFDASBgNVBAMMC3NlcnZlcl9zaWdu
MSQwIgYJKoZIhvcNAQkBFhVzZXJ2ZXJfc2lnbkBnbXNzbC5jb20wHhcNMjIxMTI4
MDYwNzQxWhcNMjMxMTI4MDYwNzQxWjCBiTELMAkGA1UEBhMCQ04xEDAOBgNVBAgM
B0JlaWppbmcxEDAOBgNVBAcMB0JlaWppbmcxDDAKBgNVBAoMA01TSTEMMAoGA1UE
CwwDbXNpMRQwEgYDVQQDDAtzZXJ2ZXJfc2lnbjEkMCIGCSqGSIb3DQEJARYVc2Vy
dmVyX3NpZ25AZ21zc2wuY29tMIIBMzCB7AYHKoZIzj0CATCB4AIBATAsBgcqhkjO
PQEBAiEA/v8AAAAA//8wRAQg/v//
//8AAAAA//wEICjp+p6dn140TVqeS89lCafzl4n1
FauPkt28vUFNlA6TBEEEMsSuLB8ZgRlfmQRGajnJlI/jC7/yZgvhcVpFiTNMdMe8
Nzai9PZ3nFm9zuNraSFT0KmHfMYqR0AC3zLlITnwoAIhAP7/
//9yA99rIcYFK1O79Ak51UEjAgEBA0IABFezx81yrCHekGL9nL8GQmhbJWyupuT7
H0qVJ7I6HVf959RMK8g4mYEI7Hf0Znh/F+WIcNeqrPgF0SLaGEN/zxIwCgYIKoZI
zj0EAwIDSQAwRgIhAKqqmjuOdloAWOJilvBl5DE8fxZUmTHmoSVTnFwD62bNAiEA
/s668Kbs3556coehyq4ffUMsoqfifgpGhsqB4HwXxYU=
-----END CERTIFICATE-----
加密
- 生成私钥
- openssl ecparam -genkey -name SM2 -param_enc explicit -outform pem -out se.key
- 生成请求
- openssl req -new -key se.key -out se.csr

- 使用ca私钥进行签名,生成加密证书
- openssl x509 -req -days 365 -in se.csr -signkey ../ca/ca.key -out se.crt
- 查看加密证书
- openssl x509 -text -in se.crt
chy-cpabe@ubuntu:~/double_certificate/first$ openssl x509 -text -in se.crt
Certificate:Data:Version: 1 (0x0)Serial Number:3c:86:77:a6:a6:08:c9:66:85:5a:01:73:aa:b4:f2:07:91:09:cc:ddSignature Algorithm: ecdsa-with-SHA256Issuer: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = server_encrypt, emailAddress = server_encrypt@gmssl.comValidityNot Before: Nov 28 06:23:08 2022 GMTNot After : Nov 28 06:23:08 2023 GMTSubject: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = server_encrypt, emailAddress = server_encrypt@gmssl.comSubject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:57:b3:c7:cd:72:ac:21:de:90:62:fd:9c:bf:06:42:68:5b:25:6c:ae:a6:e4:fb:1f:4a:95:27:b2:3a:1d:57:fd:e7:d4:4c:2b:c8:38:99:81:08:ec:77:f4:66:78:7f:17:e5:88:70:d7:aa:ac:f8:05:d1:22:da:18:43:7f:cf:12Field Type: prime-fieldPrime:00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:ffA: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:fcB: 28:e9:fa:9e:9d:9f:5e:34:4d:5a:9e:4b:cf:65:09:a7:f3:97:89:f5:15:ab:8f:92:dd:bc:bd:41:4d:94:0e:93Generator (uncompressed):04:32:c4:ae:2c:1f:19:81:19:5f:99:04:46:6a:39:c9:94:8f:e3:0b:bf:f2:66:0b:e1:71:5a:45:89:33:4c:74:c7:bc:37:36:a2:f4:f6:77:9c:59:bd:ce:e3:6b:69:21:53:d0:a9:87:7c:c6:2a:47:40:02:df:32:e5:21:39:f0:a0Order: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:72:03:df:6b:21:c6:05:2b:53:bb:f4:09:39:d5:41:23Cofactor: 1 (0x1)Signature Algorithm: ecdsa-with-SHA25630:45:02:21:00:a9:49:7c:5c:27:3f:91:54:f2:89:d4:a5:aa:45:f4:56:88:eb:d6:f7:0e:51:af:ab:df:e6:16:62:0e:62:e2:d9:02:20:3f:e2:75:c4:84:a3:64:69:c5:d3:1a:22:4b:10:77:70:1d:09:c7:70:67:7e:65:cc:71:00:ef:8f:61:5e:36:9e
-----BEGIN CERTIFICATE-----
MIIC9zCCAp0CFDyGd6amCMlmhVoBc6q08geRCczdMAoGCCqGSM49BAMCMIGPMQsw
CQYDVQQGEwJDTjEQMA4GA1UECAwHQmVpamluZzEQMA4GA1UEBwwHQmVpamluZzEM
MAoGA1UECgwDTVNJMQwwCgYDVQQLDANtc2kxFzAVBgNVBAMMDnNlcnZlcl9lbmNy
eXB0MScwJQYJKoZIhvcNAQkBFhhzZXJ2ZXJfZW5jcnlwdEBnbXNzbC5jb20wHhcN
MjIxMTI4MDYyMzA4WhcNMjMxMTI4MDYyMzA4WjCBjzELMAkGA1UEBhMCQ04xEDAO
BgNVBAgMB0JlaWppbmcxEDAOBgNVBAcMB0JlaWppbmcxDDAKBgNVBAoMA01TSTEM
MAoGA1UECwwDbXNpMRcwFQYDVQQDDA5zZXJ2ZXJfZW5jcnlwdDEnMCUGCSqGSIb3
DQEJARYYc2VydmVyX2VuY3J5cHRAZ21zc2wuY29tMIIBMzCB7AYHKoZIzj0CATCB
4AIBATAsBgcqhkjOPQEBAiEA/v8AAAAA
//8wRAQg/v8AAAAA//wEICjp+p6dn140
TVqeS89lCafzl4n1FauPkt28vUFNlA6TBEEEMsSuLB8ZgRlfmQRGajnJlI/jC7/y
ZgvhcVpFiTNMdMe8Nzai9PZ3nFm9zuNraSFT0KmHfMYqR0AC3zLlITnwoAIhAP//
//7///9yA99rIcYFK1O79Ak51UEjAgEBA0IABFezx81yrCHekGL9
nL8GQmhbJWyupuT7H0qVJ7I6HVf959RMK8g4mYEI7Hf0Znh/F+WIcNeqrPgF0SLa
GEN/zxIwCgYIKoZIzj0EAwIDSAAwRQIhAKlJfFwnP5FU8onUpapF9FaI69b3DlGv
q9/mFmIOYuLZAiA/4nXEhKNkacXTGiJLEHdwHQnHcGd+ZcxxAO+PYV42ng==
-----END CERTIFICATE-----
客户端
签名
- 生成私钥
- openssl ecparam -genkey -name SM2 -param_enc explicit -outform pem -out cs.key
- 生成请求
- openssl req -new -key cs.key -out cs.csr

- 使用ca私钥进行签名,生成加密证书
- openssl x509 -req -days 365 -in cs.csr -signkey ../ca/ca.key -out cs.crt
- 查看加密证书
- openssl x509 -text -in cs.crt
chy-cpabe@ubuntu:~/double_certificate/second$ openssl x509 -text -in cs.crt
Certificate:Data:Version: 1 (0x0)Serial Number:2e:6c:49:b9:b6:6d:42:b6:aa:5e:40:4d:94:da:49:3d:d4:ec:69:4cSignature Algorithm: ecdsa-with-SHA256Issuer: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = client_sign, emailAddress = client_sign@gmssl.comValidityNot Before: Nov 28 06:30:09 2022 GMTNot After : Nov 28 06:30:09 2023 GMTSubject: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = client_sign, emailAddress = client_sign@gmssl.comSubject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:57:b3:c7:cd:72:ac:21:de:90:62:fd:9c:bf:06:42:68:5b:25:6c:ae:a6:e4:fb:1f:4a:95:27:b2:3a:1d:57:fd:e7:d4:4c:2b:c8:38:99:81:08:ec:77:f4:66:78:7f:17:e5:88:70:d7:aa:ac:f8:05:d1:22:da:18:43:7f:cf:12Field Type: prime-fieldPrime:00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:ffA: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:fcB: 28:e9:fa:9e:9d:9f:5e:34:4d:5a:9e:4b:cf:65:09:a7:f3:97:89:f5:15:ab:8f:92:dd:bc:bd:41:4d:94:0e:93Generator (uncompressed):04:32:c4:ae:2c:1f:19:81:19:5f:99:04:46:6a:39:c9:94:8f:e3:0b:bf:f2:66:0b:e1:71:5a:45:89:33:4c:74:c7:bc:37:36:a2:f4:f6:77:9c:59:bd:ce:e3:6b:69:21:53:d0:a9:87:7c:c6:2a:47:40:02:df:32:e5:21:39:f0:a0Order: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:72:03:df:6b:21:c6:05:2b:53:bb:f4:09:39:d5:41:23Cofactor: 1 (0x1)Signature Algorithm: ecdsa-with-SHA25630:45:02:21:00:b3:b8:70:98:4c:cc:b5:e5:da:3f:c2:2a:0b:77:e4:85:4b:0e:b2:df:7d:a0:43:77:d3:e3:b6:47:e2:3c:6b:03:02:20:7e:fb:d0:84:12:08:0e:a8:3a:69:5e:f9:58:ad:d6:13:d1:54:f8:16:bd:a2:0f:07:1b:c6:83:d4:8e:49:29:95
-----BEGIN CERTIFICATE-----
MIIC6zCCApECFC5sSbm2bUK2ql5ATZTaST3U7GlMMAoGCCqGSM49BAMCMIGJMQsw
CQYDVQQGEwJDTjEQMA4GA1UECAwHQmVpamluZzEQMA4GA1UEBwwHQmVpamluZzEM
MAoGA1UECgwDTVNJMQwwCgYDVQQLDANtc2kxFDASBgNVBAMMC2NsaWVudF9zaWdu
MSQwIgYJKoZIhvcNAQkBFhVjbGllbnRfc2lnbkBnbXNzbC5jb20wHhcNMjIxMTI4
MDYzMDA5WhcNMjMxMTI4MDYzMDA5WjCBiTELMAkGA1UEBhMCQ04xEDAOBgNVBAgM
B0JlaWppbmcxEDAOBgNVBAcMB0JlaWppbmcxDDAKBgNVBAoMA01TSTEMMAoGA1UE
CwwDbXNpMRQwEgYDVQQDDAtjbGllbnRfc2lnbjEkMCIGCSqGSIb3DQEJARYVY2xp
ZW50X3NpZ25AZ21zc2wuY29tMIIBMzCB7AYHKoZIzj0CATCB4AIBATAsBgcqhkjO
PQEBAiEA/v8AAAAA//8wRAQg/v//
//8AAAAA//wEICjp+p6dn140TVqeS89lCafzl4n1
FauPkt28vUFNlA6TBEEEMsSuLB8ZgRlfmQRGajnJlI/jC7/yZgvhcVpFiTNMdMe8
Nzai9PZ3nFm9zuNraSFT0KmHfMYqR0AC3zLlITnwoAIhAP7/
//9yA99rIcYFK1O79Ak51UEjAgEBA0IABFezx81yrCHekGL9nL8GQmhbJWyupuT7
H0qVJ7I6HVf959RMK8g4mYEI7Hf0Znh/F+WIcNeqrPgF0SLaGEN/zxIwCgYIKoZI
zj0EAwIDSAAwRQIhALO4cJhMzLXl2j/CKgt35IVLDrLffaBDd9PjtkfiPGsDAiB+
+9CEEggOqDppXvlYrdYT0VT4Fr2iDwcbxoPUjkkplQ==
-----END CERTIFICATE-----
加密
- 生成私钥
- openssl ecparam -genkey -name SM2 -param_enc explicit -outform pem -out ce.key
- 生成请求
- openssl req -new -key ce.key -out ce.csr

- 使用ca私钥进行签名,生成加密证书
- openssl x509 -req -days 365 -in ce.csr -signkey ../ca/ca.key -out ce.crt
- 查看加密证书
- openssl x509 -text -in ce.crt
chy-cpabe@ubuntu:~/double_certificate/second$ openssl x509 -text -in ce.crt
Certificate:Data:Version: 1 (0x0)Serial Number:ac:9b:ca:be:a9:7a:4b:5e:fe:6f:e3:4c:05:ad:3f:e5:c0:c3:9cSignature Algorithm: ecdsa-with-SHA256Issuer: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = client_encrypt, emailAddress = client_encrypt@gmssl.comValidityNot Before: Nov 28 06:33:09 2022 GMTNot After : Nov 28 06:33:09 2023 GMTSubject: C = CN, ST = Beijing, L = Beijing, O = MSI, OU = msi, CN = client_encrypt, emailAddress = client_encrypt@gmssl.comSubject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:57:b3:c7:cd:72:ac:21:de:90:62:fd:9c:bf:06:42:68:5b:25:6c:ae:a6:e4:fb:1f:4a:95:27:b2:3a:1d:57:fd:e7:d4:4c:2b:c8:38:99:81:08:ec:77:f4:66:78:7f:17:e5:88:70:d7:aa:ac:f8:05:d1:22:da:18:43:7f:cf:12Field Type: prime-fieldPrime:00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:ffA: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:00:00:00:00:ff:ff:ff:ff:ff:ff:ff:fcB: 28:e9:fa:9e:9d:9f:5e:34:4d:5a:9e:4b:cf:65:09:a7:f3:97:89:f5:15:ab:8f:92:dd:bc:bd:41:4d:94:0e:93Generator (uncompressed):04:32:c4:ae:2c:1f:19:81:19:5f:99:04:46:6a:39:c9:94:8f:e3:0b:bf:f2:66:0b:e1:71:5a:45:89:33:4c:74:c7:bc:37:36:a2:f4:f6:77:9c:59:bd:ce:e3:6b:69:21:53:d0:a9:87:7c:c6:2a:47:40:02:df:32:e5:21:39:f0:a0Order: 00:ff:ff:ff:fe:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:ff:72:03:df:6b:21:c6:05:2b:53:bb:f4:09:39:d5:41:23Cofactor: 1 (0x1)Signature Algorithm: ecdsa-with-SHA25630:44:02:20:4a:8e:f4:1c:79:40:95:93:ea:13:30:d5:96:78:20:62:59:8c:35:66:55:68:b1:1a:4c:cb:82:74:b9:71:2e:a2:02:20:75:b7:57:c3:ba:37:11:c7:57:7a:6a:6f:68:e5:bc:a3:c9:2c:2b:69:95:f0:2d:79:4c:d1:e8:aa:57:fd:a0:dd
-----BEGIN CERTIFICATE-----
MIIC9jCCAp0CFACsm8q+qXpLXv5v40wFrT/lwMOcMAoGCCqGSM49BAMCMIGPMQsw
CQYDVQQGEwJDTjEQMA4GA1UECAwHQmVpamluZzEQMA4GA1UEBwwHQmVpamluZzEM
MAoGA1UECgwDTVNJMQwwCgYDVQQLDANtc2kxFzAVBgNVBAMMDmNsaWVudF9lbmNy
eXB0MScwJQYJKoZIhvcNAQkBFhhjbGllbnRfZW5jcnlwdEBnbXNzbC5jb20wHhcN
MjIxMTI4MDYzMzA5WhcNMjMxMTI4MDYzMzA5WjCBjzELMAkGA1UEBhMCQ04xEDAO
BgNVBAgMB0JlaWppbmcxEDAOBgNVBAcMB0JlaWppbmcxDDAKBgNVBAoMA01TSTEM
MAoGA1UECwwDbXNpMRcwFQYDVQQDDA5jbGllbnRfZW5jcnlwdDEnMCUGCSqGSIb3
DQEJARYYY2xpZW50X2VuY3J5cHRAZ21zc2wuY29tMIIBMzCB7AYHKoZIzj0CATCB
4AIBATAsBgcqhkjOPQEBAiEA/v8AAAAA
//8wRAQg/v8AAAAA//wEICjp+p6dn140
TVqeS89lCafzl4n1FauPkt28vUFNlA6TBEEEMsSuLB8ZgRlfmQRGajnJlI/jC7/y
ZgvhcVpFiTNMdMe8Nzai9PZ3nFm9zuNraSFT0KmHfMYqR0AC3zLlITnwoAIhAP//
//7///9yA99rIcYFK1O79Ak51UEjAgEBA0IABFezx81yrCHekGL9
nL8GQmhbJWyupuT7H0qVJ7I6HVf959RMK8g4mYEI7Hf0Znh/F+WIcNeqrPgF0SLa
GEN/zxIwCgYIKoZIzj0EAwIDRwAwRAIgSo70HHlAlZPqEzDVlnggYlmMNWZVaLEa
TMuCdLlxLqICIHW3V8O6NxHHV3pqb2jlvKPJLCtplfAteUzR6KpX/aDd
-----END CERTIFICATE-----
层次结构

测试未通过,报错信息如下:
- 140524443496448:error:0B080074:x509 certificate routines:X509_check_private_key:key values mismatch:crypto/x509/x509_cmp.c:288:
- 140622668791808:error:1417A0C1:SSL routines:tls_post_process_client_hello:no shared cipher:ssl/statem/statem_srvr.c:1502:
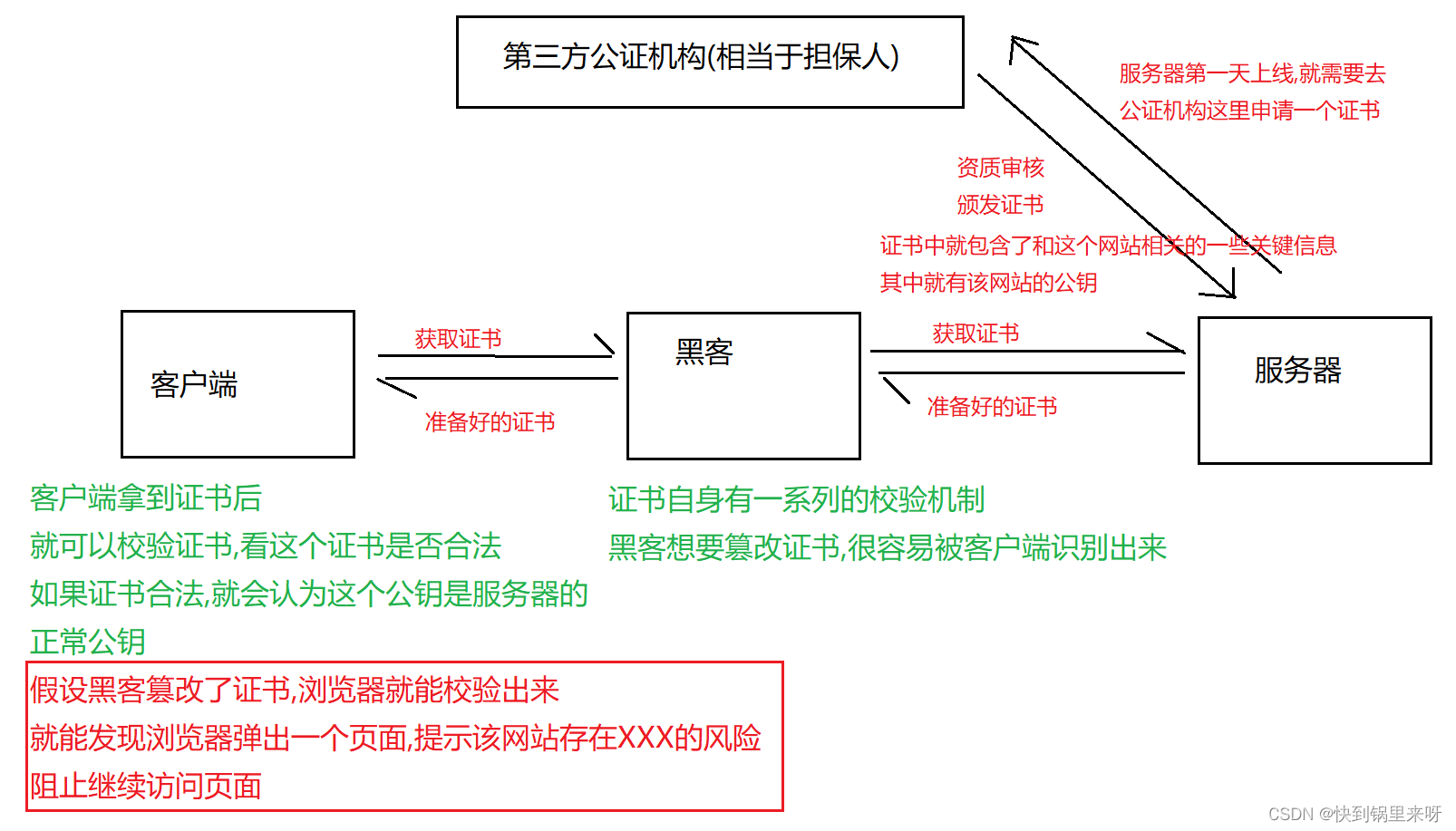
错误分析
- 需要修改配置文件openssl.cnf,从而开启证书的keyUsage字段,实现签名和加密证书的区分
- 给用户生成证书的时候,不仅要使用-CA指定证书,还需要使用-CAKey指定CA的私钥
- 不知道是否合规:将证书和私钥存储在同一个文件中;这条命令不是必须的,双向认证并未使用包含私钥的证书文件,其目的是用于格式转换
不理解(后期弥补)
- 不理解:生成请求数据,无论是客户端服务端的签名加密,均使用根证书,多了一条-newkey ec:根证书.pem -new;此外,在成成证书的时候,使用的是CA的key和证书,ca是由根推出来的。延长证书链???
- 不理解:生成证书的时候使用 -extensions v3_req \ 就能实现签名/加密的区分??
- 不理解:-CAcreateserial 的含义是啥?
错误的内容 -> 结束
正确的开始
目录层级

自动化脚本
SM2certgen.sh
# For a list of supported curves, use "apps/openssl ecparam -list_curves".# Path to the openssl distribution
OPENSSL_DIR=.
# Path to the openssl program
OPENSSL_CMD=gmssl
# Option to find configuration file
OPENSSL_CNF="-config ./openssl.cnf"
# Directory where certificates are stored
CERTS_DIR=./sm2Certs
# Directory where private key files are stored
KEYS_DIR=$CERTS_DIR
# Directory where combo files (containing a certificate and corresponding
# private key together) are stored
COMBO_DIR=$CERTS_DIR
# cat command
echo "start"
#Win
#CAT="C:/Progra~1/Git/usr/bin/cat.exe"
# rm command
#RM="C:/Progra~1/Git/usr/bin/rm.exe"
# mkdir command
#MKDIR="C:/Progra~1/Git/usr/bin/mkdir.exe"
#Linux
CAT=cat
# rm command
RM=rm
# mkdir command
MKDIR=mkdir
echo "end"
# The certificate will expire these many days after the issue date.
DAYS=1500
TEST_CA_CURVE=SM2
TEST_CA_FILE=CA
TEST_CA_DN="//skip=yes/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)"TEST_SERVER_CURVE=SM2
TEST_SERVER_FILE=SS
TEST_SERVER_DN="//skip=yes/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=server sign (SM2)"TEST_SERVER_ENC_FILE=SE
TEST_SERVER_ENC_DN="//skip=yes/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=server enc (SM2)"TEST_CLIENT_CURVE=SM2
TEST_CLIENT_FILE=CS
TEST_CLIENT_DN="//skip=yes/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=client sign (SM2)"TEST_CLIENT_ENC_FILE=CE
TEST_CLIENT_ENC_DN="//skip=yes/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=client enc (SM2)"# Generating an EC certificate involves the following main steps
# 1. Generating curve parameters (if needed)
# 2. Generating a certificate request
# 3. Signing the certificate request
# 4. [Optional] One can combine the cert and private key into a single
# file and also delete the certificate request$MKDIR -p $CERTS_DIR
$MKDIR -p $KEYS_DIR
$MKDIR -p $COMBO_DIRecho "Generating self-signed CA certificate (on curve $TEST_CA_CURVE)"
echo "==============================================================="
$OPENSSL_CMD ecparam -name $TEST_CA_CURVE -out $TEST_CA_CURVE.pem# Generate a new certificate request in $TEST_CA_FILE.req.pem. A
# new ecdsa (actually ECC) key pair is generated on the parameters in
# $TEST_CA_CURVE.pem and the private key is saved in $TEST_CA_FILE.key.pem
# WARNING: By using the -nodes option, we force the private key to be
# stored in the clear (rather than encrypted with a password).# 在$TEST_CA_FILE.req.pem中生成一个新的证书请求。在$TEST_CA_CURVE中的参数上
# 生成一个新的ecdsa(实际上是ECC)密钥对。私钥保存在“$TEST_CA_FILE.key”文件中。
# 通过使用-nodes选项,我们强制将私钥存储在clear中(而不是用密码加密)。$OPENSSL_CMD req $OPENSSL_CNF -nodes -subj "$TEST_CA_DN" \-keyout $KEYS_DIR/$TEST_CA_FILE.key.pem \-newkey ec:$TEST_CA_CURVE.pem -new \-out $CERTS_DIR/$TEST_CA_FILE.req.pem# Sign the certificate request in $TEST_CA_FILE.req.pem using the
# private key in $TEST_CA_FILE.key.pem and include the CA extension.
# Make the certificate valid for 1500 days from the time of signing.
# The certificate is written into $TEST_CA_FILE.cert.pem# 在$TEST_CA_FILE.req中签名证书请求。使用$TEST_CA_FILE.key中的私钥生成pem,
# 并包含CA扩展名。证书有效期为自签署之日起1500天。
# 证书被写入$TEST_CA_FILE.cert.pem
$OPENSSL_CMD x509 -req -days $DAYS \-in $CERTS_DIR/$TEST_CA_FILE.req.pem \-extfile $OPENSSL_DIR/openssl.cnf \-extensions v3_ca \-signkey $KEYS_DIR/$TEST_CA_FILE.key.pem \-out $CERTS_DIR/$TEST_CA_FILE.cert.pem# Display the certificate
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_CA_FILE.cert.pem -text# Place the certificate and key in a common file
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_CA_FILE.cert.pem -issuer -subject \> $COMBO_DIR/$TEST_CA_FILE.pem
$CAT $KEYS_DIR/$TEST_CA_FILE.key.pem >> $COMBO_DIR/$TEST_CA_FILE.pem# Remove the cert request file (no longer needed)
$RM $CERTS_DIR/$TEST_CA_FILE.req.pemecho "GENERATING A TEST SERVER CERTIFICATE (on elliptic curve $TEST_SERVER_CURVE)"
echo "=========================================================================="
# Generate a new certificate request in $TEST_SERVER_FILE.req.pem. A
# new ecdsa (actually ECC) key pair is generated on the parameters in
# $TEST_SERVER_CURVE.pem and the private key is saved in
# $TEST_SERVER_FILE.key.pem
# WARNING: By using the -nodes option, we force the private key to be
# stored in the clear (rather than encrypted with a password).#在$TEST_SERVER_FILE.req.pem中生成新的证书请求。在$TEST_SERVER_CURVE中的
#参数上生成一个新的ecdsa(实际上是ECC)密钥对。私钥保存在“$TEST_SERVER_FILE.key”文
#件中。pemWARNING:通过使用-nodes选项,我们强制将私钥存储在clear中
#(而不是使用密码进行加密)。#TEST_SERVER_DN -> server的签名 SS
$OPENSSL_CMD req $OPENSSL_CNF -nodes -subj "$TEST_SERVER_DN" \-keyout $KEYS_DIR/$TEST_SERVER_FILE.key.pem \-newkey ec:$TEST_SERVER_CURVE.pem -new \-out $CERTS_DIR/$TEST_SERVER_FILE.req.pem# Sign the certificate request in $TEST_SERVER_FILE.req.pem using the
# CA certificate in $TEST_CA_FILE.cert.pem and the CA private key in
# $TEST_CA_FILE.key.pem. Since we do not have an existing serial number
# file for this CA, create one. Make the certificate valid for $DAYS days
# from the time of signing. The certificate is written into
# $TEST_SERVER_FILE.cert.pem
$OPENSSL_CMD x509 -req -days $DAYS \-in $CERTS_DIR/$TEST_SERVER_FILE.req.pem \-CA $CERTS_DIR/$TEST_CA_FILE.cert.pem \-CAkey $KEYS_DIR/$TEST_CA_FILE.key.pem \-extfile $OPENSSL_DIR/openssl.cnf \-extensions v3_req \-out $CERTS_DIR/$TEST_SERVER_FILE.cert.pem -CAcreateserial# Display the certificate
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_SERVER_FILE.cert.pem -text# Place the certificate and key in a common file
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_SERVER_FILE.cert.pem -issuer -subject \> $COMBO_DIR/$TEST_SERVER_FILE.pem
$CAT $KEYS_DIR/$TEST_SERVER_FILE.key.pem >> $COMBO_DIR/$TEST_SERVER_FILE.pem# Remove the cert request file (no longer needed)
$RM $CERTS_DIR/$TEST_SERVER_FILE.req.pemecho " GENERATING A TEST SERVER ENCRYPT CERTIFICATE (on elliptic curve $TEST_SERVER_CURVE)"
echo " ==================================================================================="
# Generate a new certificate request in $TEST_SERVER_FILE.req.pem. A
# new ecdsa (actually ECC) key pair is generated on the parameters in
# $TEST_SERVER_CURVE.pem and the private key is saved in
# $TEST_SERVER_FILE.key.pem
# WARNING: By using the -nodes option, we force the private key to be
# stored in the clear (rather than encrypted with a password).
$OPENSSL_CMD req $OPENSSL_CNF -nodes -subj "$TEST_SERVER_ENC_DN" \-keyout $KEYS_DIR/$TEST_SERVER_ENC_FILE.key.pem \-newkey ec:$TEST_SERVER_CURVE.pem -new \-out $CERTS_DIR/$TEST_SERVER_ENC_FILE.req.pem# Sign the certificate request in $TEST_SERVER_FILE.req.pem using the
# CA certificate in $TEST_CA_FILE.cert.pem and the CA private key in
# $TEST_CA_FILE.key.pem. Since we do not have an existing serial number
# file for this CA, create one. Make the certificate valid for $DAYS days
# from the time of signing. The certificate is written into
# $TEST_SERVER_FILE.cert.pem
$OPENSSL_CMD x509 -req -days $DAYS \-in $CERTS_DIR/$TEST_SERVER_ENC_FILE.req.pem \-CA $CERTS_DIR/$TEST_CA_FILE.cert.pem \-CAkey $KEYS_DIR/$TEST_CA_FILE.key.pem \-extfile $OPENSSL_DIR/openssl.cnf \-extensions v3enc_req \-out $CERTS_DIR/$TEST_SERVER_ENC_FILE.cert.pem -CAcreateserial# Display the certificate
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_SERVER_ENC_FILE.cert.pem -text# Place the certificate and key in a common file
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_SERVER_ENC_FILE.cert.pem -issuer -subject \> $COMBO_DIR/$TEST_SERVER_ENC_FILE.pem
$CAT $KEYS_DIR/$TEST_SERVER_ENC_FILE.key.pem >> $COMBO_DIR/$TEST_SERVER_ENC_FILE.pem# Remove the cert request file (no longer needed)
$RM $CERTS_DIR/$TEST_SERVER_ENC_FILE.req.pemecho "GENERATING A TEST CLIENT CERTIFICATE (on elliptic curve $TEST_CLIENT_CURVE)"
echo "=========================================================================="
# Generate a new certificate request in $TEST_CLIENT_FILE.req.pem. A
# new ecdsa (actually ECC) key pair is generated on the parameters in
# $TEST_CLIENT_CURVE.pem and the private key is saved in
# $TEST_CLIENT_FILE.key.pem
# WARNING: By using the -nodes option, we force the private key to be
# stored in the clear (rather than encrypted with a password).
$OPENSSL_CMD req $OPENSSL_CNF -nodes -subj "$TEST_CLIENT_DN" \-keyout $KEYS_DIR/$TEST_CLIENT_FILE.key.pem \-newkey ec:$TEST_CLIENT_CURVE.pem -new \-out $CERTS_DIR/$TEST_CLIENT_FILE.req.pem# Sign the certificate request in $TEST_CLIENT_FILE.req.pem using the
# CA certificate in $TEST_CA_FILE.cert.pem and the CA private key in
# $TEST_CA_FILE.key.pem. Since we do not have an existing serial number
# file for this CA, create one. Make the certificate valid for $DAYS days
# from the time of signing. The certificate is written into
# $TEST_CLIENT_FILE.cert.pem
$OPENSSL_CMD x509 -req -days $DAYS \-in $CERTS_DIR/$TEST_CLIENT_FILE.req.pem \-CA $CERTS_DIR/$TEST_CA_FILE.cert.pem \-CAkey $KEYS_DIR/$TEST_CA_FILE.key.pem \-extfile $OPENSSL_DIR/openssl.cnf \-extensions v3_req \-out $CERTS_DIR/$TEST_CLIENT_FILE.cert.pem -CAcreateserial# Display the certificate
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_CLIENT_FILE.cert.pem -text# Place the certificate and key in a common file
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_CLIENT_FILE.cert.pem -issuer -subject \> $COMBO_DIR/$TEST_CLIENT_FILE.pem
$CAT $KEYS_DIR/$TEST_CLIENT_FILE.key.pem >> $COMBO_DIR/$TEST_CLIENT_FILE.pem# Remove the cert request file (no longer needed)
$RM $CERTS_DIR/$TEST_CLIENT_FILE.req.pemecho " GENERATING A TEST CLIENT ENCRYPT CERTIFICATE (on elliptic curve $TEST_CLIENT_CURVE)"
echo " ==================================================================================="
# Generate a new certificate request in $TEST_CLIENT_FILE.req.pem. A
# new ecdsa (actually ECC) key pair is generated on the parameters in
# $TEST_CLIENT_CURVE.pem and the private key is saved in
# $TEST_CLIENT_FILE.key.pem
# WARNING: By using the -nodes option, we force the private key to be
# stored in the clear (rather than encrypted with a password).
$OPENSSL_CMD req $OPENSSL_CNF -nodes -subj "$TEST_CLIENT_ENC_DN" \-keyout $KEYS_DIR/$TEST_CLIENT_ENC_FILE.key.pem \-newkey ec:$TEST_CLIENT_CURVE.pem -new \-out $CERTS_DIR/$TEST_CLIENT_ENC_FILE.req.pem# Sign the certificate request in $TEST_CLIENT_FILE.req.pem using the
# CA certificate in $TEST_CA_FILE.cert.pem and the CA private key in
# $TEST_CA_FILE.key.pem. Since we do not have an existing serial number
# file for this CA, create one. Make the certificate valid for $DAYS days
# from the time of signing. The certificate is written into
# $TEST_CLIENT_FILE.cert.pem
$OPENSSL_CMD x509 -req -days $DAYS \-in $CERTS_DIR/$TEST_CLIENT_ENC_FILE.req.pem \-CA $CERTS_DIR/$TEST_CA_FILE.cert.pem \-CAkey $KEYS_DIR/$TEST_CA_FILE.key.pem \-extfile $OPENSSL_DIR/openssl.cnf \-extensions v3enc_req \-out $CERTS_DIR/$TEST_CLIENT_ENC_FILE.cert.pem -CAcreateserial# Display the certificate
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_CLIENT_ENC_FILE.cert.pem -text# Place the certificate and key in a common file
$OPENSSL_CMD x509 -in $CERTS_DIR/$TEST_CLIENT_ENC_FILE.cert.pem -issuer -subject \> $COMBO_DIR/$TEST_CLIENT_ENC_FILE.pem
$CAT $KEYS_DIR/$TEST_CLIENT_ENC_FILE.key.pem >> $COMBO_DIR/$TEST_CLIENT_ENC_FILE.pem# Remove the cert request file (no longer needed)
$RM $CERTS_DIR/$TEST_CLIENT_ENC_FILE.req.pem
openssl.cnf
- openssl.cnf 和上面的SM2certgen.sh放置在同级目录
#
# OpenSSL example configuration file.
# This is mostly being used for generation of certificate requests.
## This definition stops the following lines choking if HOME isn't
# defined.
HOME = .
RANDFILE = $ENV::HOME/.rnd# Extra OBJECT IDENTIFIER info:
#oid_file = $ENV::HOME/.oid
oid_section = new_oids# To use this configuration file with the "-extfile" option of the
# "openssl x509" utility, name here the section containing the
# X.509v3 extensions to use:
# extensions =
# (Alternatively, use a configuration file that has only
# X.509v3 extensions in its main [= default] section.)[ new_oids ]# We can add new OIDs in here for use by 'ca', 'req' and 'ts'.
# Add a simple OID like this:
# testoid1=1.2.3.4
# Or use config file substitution like this:
# testoid2=${testoid1}.5.6# Policies used by the TSA examples.
tsa_policy1 = 1.2.3.4.1
tsa_policy2 = 1.2.3.4.5.6
tsa_policy3 = 1.2.3.4.5.7####################################################################
[ ca ]
default_ca = CA_default # The default ca section####################################################################
[ CA_default ]dir = ./demoCA # Where everything is kept
certs = $dir/certs # Where the issued certs are kept
crl_dir = $dir/crl # Where the issued crl are kept
database = $dir/index.txt # database index file.
#unique_subject = no # Set to 'no' to allow creation of# several ctificates with same subject.
new_certs_dir = $dir/newcerts # default place for new certs.certificate = $dir/cacert.pem # The CA certificate
serial = $dir/serial # The current serial number
crlnumber = $dir/crlnumber # the current crl number# must be commented out to leave a V1 CRL
crl = $dir/crl.pem # The current CRL
private_key = $dir/private/cakey.pem # The private key
RANDFILE = $dir/private/.rand # private random number filex509_extensions = usr_cert # The extentions to add to the cert# Comment out the following two lines for the "traditional"
# (and highly broken) format.
name_opt = ca_default # Subject Name options
cert_opt = ca_default # Certificate field options# Extension copying option: use with caution.
# copy_extensions = copy# Extensions to add to a CRL. Note: Netscape communicator chokes on V2 CRLs
# so this is commented out by default to leave a V1 CRL.
# crlnumber must also be commented out to leave a V1 CRL.
# crl_extensions = crl_extdefault_days = 365 # how long to certify for
default_crl_days= 30 # how long before next CRL
default_md = default # use public key default MD
preserve = no # keep passed DN ordering# A few difference way of specifying how similar the request should look
# For type CA, the listed attributes must be the same, and the optional
# and supplied fields are just that :-)
policy = policy_match# For the CA policy
[ policy_match ]
countryName = match
stateOrProvinceName = match
organizationName = match
organizationalUnitName = optional
commonName = supplied
emailAddress = optional# For the 'anything' policy
# At this point in time, you must list all acceptable 'object'
# types.
[ policy_anything ]
countryName = optional
stateOrProvinceName = optional
localityName = optional
organizationName = optional
organizationalUnitName = optional
commonName = supplied
emailAddress = optional####################################################################
[ req ]
default_bits = 2048
default_md = sm3
default_keyfile = privkey.pem
distinguished_name = req_distinguished_name
attributes = req_attributes
x509_extensions = v3_ca # The extentions to add to the self signed cert# Passwords for private keys if not present they will be prompted for
# input_password = secret
# output_password = secret# This sets a mask for permitted string types. There are several options.
# default: PrintableString, T61String, BMPString.
# pkix : PrintableString, BMPString (PKIX recommendation before 2004)
# utf8only: only UTF8Strings (PKIX recommendation after 2004).
# nombstr : PrintableString, T61String (no BMPStrings or UTF8Strings).
# MASK:XXXX a literal mask value.
# WARNING: ancient versions of Netscape crash on BMPStrings or UTF8Strings.
string_mask = utf8only# req_extensions = v3_req # The extensions to add to a certificate request[ req_distinguished_name ]
countryName = Country Name (2 letter code)
countryName_default = XX
countryName_min = 2
countryName_max = 2stateOrProvinceName = State or Province Name (full name)
#stateOrProvinceName_default = Default ProvincelocalityName = Locality Name (eg, city)
localityName_default = Default City0.organizationName = Organization Name (eg, company)
0.organizationName_default = Default Company Ltd# we can do this but it is not needed normally :-)
#1.organizationName = Second Organization Name (eg, company)
#1.organizationName_default = World Wide Web Pty LtdorganizationalUnitName = Organizational Unit Name (eg, section)
#organizationalUnitName_default =commonName = Common Name (eg, your name or your server\'s hostname)
commonName_max = 64emailAddress = Email Address
emailAddress_max = 64# SET-ex3 = SET extension number 3[ req_attributes ]
challengePassword = A challenge password
challengePassword_min = 4
challengePassword_max = 20unstructuredName = An optional company name[ usr_cert ]# These extensions are added when 'ca' signs a request.# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.basicConstraints=CA:FALSE# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.# This is OK for an SSL server.
# nsCertType = server# For an object signing certificate this would be used.
# nsCertType = objsign# For normal client use this is typical
# nsCertType = client, email# and for everything including object signing:
# nsCertType = client, email, objsignkeyCertSign# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment dataEncipherment keyAgreement keyCertSign encipherOnly cRLSign decipherOnly# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move# Copy subject details
# issuerAltName=issuer:copy#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName# This is required for TSA certificates.
# extendedKeyUsage = critical,timeStamping[ v3_req ]# Extensions to add to a certificate requestbasicConstraints = CA:FALSE
keyUsage = nonRepudiation, digitalSignature[ v3enc_req ]# Extensions to add to a certificate requestbasicConstraints = CA:FALSE
keyUsage = keyAgreement, keyEncipherment, dataEncipherment[ v3_ca ]# Extensions for a typical CA# PKIX recommendation.subjectKeyIdentifier=hashauthorityKeyIdentifier=keyid:always,issuer# This is what PKIX recommends but some broken software chokes on critical
# extensions.
#basicConstraints = critical,CA:true
# So we do this instead.
basicConstraints = CA:true# Key usage: this is typical for a CA certificate. However since it will
# prevent it being used as an test self-signed certificate it is best
# left out by default.
keyUsage = cRLSign, keyCertSign# Some might want this also
# nsCertType = sslCA, emailCA# Include email address in subject alt name: another PKIX recommendation
# subjectAltName=email:copy
# Copy issuer details
# issuerAltName=issuer:copy# DER hex encoding of an extension: beware experts only!
# obj=DER:02:03
# Where 'obj' is a standard or added object
# You can even override a supported extension:
# basicConstraints= critical, DER:30:03:01:01:FF[ crl_ext ]# CRL extensions.
# Only issuerAltName and authorityKeyIdentifier make any sense in a CRL.# issuerAltName=issuer:copy
authorityKeyIdentifier=keyid:always[ proxy_cert_ext ]
# These extensions should be added when creating a proxy certificate# This goes against PKIX guidelines but some CAs do it and some software
# requires this to avoid interpreting an end user certificate as a CA.basicConstraints=CA:FALSE# Here are some examples of the usage of nsCertType. If it is omitted
# the certificate can be used for anything *except* object signing.# This is OK for an SSL server.
# nsCertType = server# For an object signing certificate this would be used.
# nsCertType = objsign# For normal client use this is typical
# nsCertType = client, email# and for everything including object signing:
# nsCertType = client, email, objsign# This is typical in keyUsage for a client certificate.
# keyUsage = nonRepudiation, digitalSignature, keyEncipherment# This will be displayed in Netscape's comment listbox.
nsComment = "OpenSSL Generated Certificate"# PKIX recommendations harmless if included in all certificates.
subjectKeyIdentifier=hash
authorityKeyIdentifier=keyid,issuer# This stuff is for subjectAltName and issuerAltname.
# Import the email address.
# subjectAltName=email:copy
# An alternative to produce certificates that aren't
# deprecated according to PKIX.
# subjectAltName=email:move# Copy subject details
# issuerAltName=issuer:copy#nsCaRevocationUrl = http://www.domain.dom/ca-crl.pem
#nsBaseUrl
#nsRevocationUrl
#nsRenewalUrl
#nsCaPolicyUrl
#nsSslServerName# This really needs to be in place for it to be a proxy certificate.
proxyCertInfo=critical,language:id-ppl-anyLanguage,pathlen:3,policy:foo####################################################################
[ tsa ]default_tsa = tsa_config1 # the default TSA section[ tsa_config1 ]# These are used by the TSA reply generation only.
dir = ./demoCA # TSA root directory
serial = $dir/tsaserial # The current serial number (mandatory)
crypto_device = builtin # OpenSSL engine to use for signing
signer_cert = $dir/tsacert.pem # The TSA signing certificate# (optional)
certs = $dir/cacert.pem # Certificate chain to include in reply# (optional)
signer_key = $dir/private/tsakey.pem # The TSA private key (optional)default_policy = tsa_policy1 # Policy if request did not specify it# (optional)
other_policies = tsa_policy2, tsa_policy3 # acceptable policies (optional)
digests = md5, sha1 # Acceptable message digests (mandatory)
accuracy = secs:1, millisecs:500, microsecs:100 # (optional)
clock_precision_digits = 0 # number of digits after dot. (optional)
ordering = yes # Is ordering defined for timestamps?# (optional, default: no)
tsa_name = yes # Must the TSA name be included in the reply?# (optional, default: no)
ess_cert_id_chain = no # Must the ESS cert id chain be included?# (optional, default: no)
执行结果
chy-cpabe@ubuntu:~/double_certificate/test_sh$ ls
openssl.cnf SM2certGen.sh sm2Certs
chy-cpabe@ubuntu:~/double_certificate/test_sh$ ./SM2certGen.sh
start
end
Generating self-signed CA certificate (on curve SM2)
===============================================================
Generating an EC private key
writing new private key to './sm2Certs/CA.key.pem'
-----
req: Skipping unknown attribute "/skip"
Signature ok
subject=C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)
Getting Private key
Certificate:Data:Version: 3 (0x2)Serial Number:84:3a:ff:da:ac:ac:89:34Signature Algorithm: sm2sign-with-sm3Issuer: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)ValidityNot Before: Nov 28 09:48:17 2022 GMTNot After : Jan 6 09:48:17 2027 GMTSubject: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)Subject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:ce:20:49:82:a9:26:1e:9e:2c:3c:a9:71:c1:fb:cb:45:f8:ac:de:94:9f:26:25:cd:2b:0f:bd:95:59:07:91:04:1e:ac:ae:b6:04:2c:23:24:b0:b6:e2:e8:53:13:e3:cf:fc:64:71:fe:c0:46:75:57:22:e0:01:05:a6:dc:35:d1ASN1 OID: sm2p256v1NIST CURVE: SM2X509v3 extensions:X509v3 Subject Key Identifier: 46:73:BA:3D:B5:E6:DD:C1:24:48:90:92:19:3F:21:F6:53:18:5E:76X509v3 Authority Key Identifier: keyid:46:73:BA:3D:B5:E6:DD:C1:24:48:90:92:19:3F:21:F6:53:18:5E:76X509v3 Basic Constraints: CA:TRUEX509v3 Key Usage: Certificate Sign, CRL SignSignature Algorithm: sm2sign-with-sm330:44:02:20:13:30:fa:87:f3:eb:48:84:f2:19:55:a3:61:8d:63:2c:00:95:06:1b:8a:c5:d6:dd:4b:9b:01:f6:bf:21:de:65:02:20:6e:47:26:3c:f2:fe:44:7b:63:1a:82:7f:6f:e5:29:4f:b0:5d:e3:e5:33:5a:11:35:32:07:f5:08:7d:78:ab:12
-----BEGIN CERTIFICATE-----
MIICWTCCAgCgAwIBAgIJAIQ6/9qsrIk0MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGCMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDFNPUkIgb2YgVEFTUzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTBZ
MBMGByqGSM49AgEGCCqBHM9VAYItA0IABM4gSYKpJh6eLDypccH7y0X4rN6UnyYl
zSsPvZVZB5EEHqyutgQsIySwtuLoUxPjz/xkcf7ARnVXIuABBabcNdGjXTBbMB0G
A1UdDgQWBBRGc7o9tebdwSRIkJIZPyH2UxhedjAfBgNVHSMEGDAWgBRGc7o9tebd
wSRIkJIZPyH2UxhedjAMBgNVHRMEBTADAQH/MAsGA1UdDwQEAwIBBjAKBggqgRzP
VQGDdQNHADBEAiATMPqH8+tIhPIZVaNhjWMsAJUGG4rF1t1LmwH2vyHeZQIgbkcm
PPL+RHtjGoJ/b+UpT7Bd4+UzWhE1Mgf1CH14qxI=
-----END CERTIFICATE-----
GENERATING A TEST SERVER CERTIFICATE (on elliptic curve SM2)
==========================================================================
Generating an EC private key
writing new private key to './sm2Certs/SS.key.pem'
-----
req: Skipping unknown attribute "/skip"
Signature ok
subject=C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = server sign (SM2)
Getting CA Private Key
Certificate:Data:Version: 3 (0x2)Serial Number:bd:61:fb:da:53:9a:1c:39Signature Algorithm: sm2sign-with-sm3Issuer: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)ValidityNot Before: Nov 28 09:48:17 2022 GMTNot After : Jan 6 09:48:17 2027 GMTSubject: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = server sign (SM2)Subject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:81:09:0d:ec:d1:99:8f:0d:28:5f:bd:83:e1:2c:01:af:bb:f5:bc:50:9b:30:ec:f1:c6:39:4c:c0:df:50:6e:fc:6d:8e:47:3a:73:bf:2c:2a:29:da:dc:d1:8d:e1:fc:86:1f:47:9d:30:cf:0b:40:4c:82:99:f6:45:c9:8b:6a:eaASN1 OID: sm2p256v1NIST CURVE: SM2X509v3 extensions:X509v3 Basic Constraints: CA:FALSEX509v3 Key Usage: Digital Signature, Non RepudiationSignature Algorithm: sm2sign-with-sm330:45:02:21:00:e7:bc:48:a8:e3:f1:67:48:67:bd:f2:08:e7:3d:c6:e5:2a:60:2e:63:ac:08:28:09:65:04:da:ac:d6:a2:81:5c:02:20:36:cc:c9:3d:e5:37:64:52:49:de:27:6d:f7:76:47:7c:f7:8a:6d:f7:ca:e9:cf:fb:b2:6d:66:ee:42:bc:40:f5
-----BEGIN CERTIFICATE-----
MIICGzCCAcGgAwIBAgIJAL1h+9pTmhw5MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGGMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDEJTUkMgb2YgVEFTUzEaMBgGA1UEAwwRc2VydmVyIHNpZ24gKFNN
MikwWTATBgcqhkjOPQIBBggqgRzPVQGCLQNCAASBCQ3s0ZmPDShfvYPhLAGvu/W8
UJsw7PHGOUzA31Bu/G2ORzpzvywqKdrc0Y3h/IYfR50wzwtATIKZ9kXJi2rqoxow
GDAJBgNVHRMEAjAAMAsGA1UdDwQEAwIGwDAKBggqgRzPVQGDdQNIADBFAiEA57xI
qOPxZ0hnvfII5z3G5SpgLmOsCCgJZQTarNaigVwCIDbMyT3lN2RSSd4nbfd2R3z3
im33yunP+7JtZu5CvED1
-----END CERTIFICATE-----GENERATING A TEST SERVER ENCRYPT CERTIFICATE (on elliptic curve SM2)===================================================================================
Generating an EC private key
writing new private key to './sm2Certs/SE.key.pem'
-----
req: Skipping unknown attribute "/skip"
Signature ok
subject=C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = server enc (SM2)
Getting CA Private Key
Certificate:Data:Version: 3 (0x2)Serial Number:bd:61:fb:da:53:9a:1c:3aSignature Algorithm: sm2sign-with-sm3Issuer: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)ValidityNot Before: Nov 28 09:48:17 2022 GMTNot After : Jan 6 09:48:17 2027 GMTSubject: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = server enc (SM2)Subject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:bd:4b:58:9f:96:88:a7:4d:5f:b2:09:59:0d:4f:bb:dd:62:72:b0:e8:4c:a8:98:66:a3:1b:23:b9:db:ce:bc:2d:a2:1c:be:d6:dd:2d:13:bd:53:e6:6f:44:3e:4e:b6:e5:af:bc:8b:83:9b:25:66:54:dd:e3:f7:dd:20:51:29:97ASN1 OID: sm2p256v1NIST CURVE: SM2X509v3 extensions:X509v3 Basic Constraints: CA:FALSEX509v3 Key Usage: Key Encipherment, Data Encipherment, Key AgreementSignature Algorithm: sm2sign-with-sm330:45:02:21:00:9a:59:a4:58:2a:ff:d6:a4:03:b5:68:22:ec:52:44:5a:aa:49:9a:18:61:06:5c:4f:ed:dc:2c:2b:b2:62:f4:8e:02:20:29:a6:0a:8e:70:00:91:44:18:12:b6:7d:d9:c7:f9:66:16:d3:8b:6c:d4:83:99:c7:7d:67:6d:f6:94:51:b1:a8
-----BEGIN CERTIFICATE-----
MIICGjCCAcCgAwIBAgIJAL1h+9pTmhw6MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGFMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDEJTUkMgb2YgVEFTUzEZMBcGA1UEAwwQc2VydmVyIGVuYyAoU00y
KTBZMBMGByqGSM49AgEGCCqBHM9VAYItA0IABL1LWJ+WiKdNX7IJWQ1Pu91icrDo
TKiYZqMbI7nbzrwtohy+1t0tE71T5m9EPk625a+8i4ObJWZU3eP33SBRKZejGjAY
MAkGA1UdEwQCMAAwCwYDVR0PBAQDAgM4MAoGCCqBHM9VAYN1A0gAMEUCIQCaWaRY
Kv/WpAO1aCLsUkRaqkmaGGEGXE/t3CwrsmL0jgIgKaYKjnAAkUQYErZ92cf5ZhbT
i2zUg5nHfWdt9pRRsag=
-----END CERTIFICATE-----
GENERATING A TEST CLIENT CERTIFICATE (on elliptic curve SM2)
==========================================================================
Generating an EC private key
writing new private key to './sm2Certs/CS.key.pem'
-----
req: Skipping unknown attribute "/skip"
Signature ok
subject=C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = client sign (SM2)
Getting CA Private Key
Certificate:Data:Version: 3 (0x2)Serial Number:bd:61:fb:da:53:9a:1c:3bSignature Algorithm: sm2sign-with-sm3Issuer: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)ValidityNot Before: Nov 28 09:48:17 2022 GMTNot After : Jan 6 09:48:17 2027 GMTSubject: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = client sign (SM2)Subject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:d4:b3:30:f2:e8:a7:66:42:de:a4:2f:b9:5c:51:51:a6:35:ab:f3:00:df:fa:6c:7c:be:8a:cd:87:07:09:5f:b3:77:18:e6:94:c6:32:e5:a7:f6:ca:ad:b9:b6:bf:5b:04:18:d5:a2:d6:88:03:e8:a7:10:48:f5:8b:81:81:6f:a2ASN1 OID: sm2p256v1NIST CURVE: SM2X509v3 extensions:X509v3 Basic Constraints: CA:FALSEX509v3 Key Usage: Digital Signature, Non RepudiationSignature Algorithm: sm2sign-with-sm330:46:02:21:00:9c:51:38:c8:bb:0d:6f:9f:21:39:e1:fe:91:9c:e3:ec:5d:23:62:ae:ab:26:3d:be:bc:c5:2e:03:21:33:54:0a:02:21:00:d9:67:aa:55:97:ee:8f:bb:7c:fa:31:5a:bf:f5:08:1f:f2:bf:0f:2c:c8:88:90:0e:e8:95:65:5e:93:0b:35:13
-----BEGIN CERTIFICATE-----
MIICHDCCAcGgAwIBAgIJAL1h+9pTmhw7MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGGMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDEJTUkMgb2YgVEFTUzEaMBgGA1UEAwwRY2xpZW50IHNpZ24gKFNN
MikwWTATBgcqhkjOPQIBBggqgRzPVQGCLQNCAATUszDy6KdmQt6kL7lcUVGmNavz
AN/6bHy+is2HBwlfs3cY5pTGMuWn9sqtuba/WwQY1aLWiAPopxBI9YuBgW+ioxow
GDAJBgNVHRMEAjAAMAsGA1UdDwQEAwIGwDAKBggqgRzPVQGDdQNJADBGAiEAnFE4
yLsNb58hOeH+kZzj7F0jYq6rJj2+vMUuAyEzVAoCIQDZZ6pVl+6Pu3z6MVq/9Qgf
8r8PLMiIkA7olWVekws1Ew==
-----END CERTIFICATE-----GENERATING A TEST CLIENT ENCRYPT CERTIFICATE (on elliptic curve SM2)===================================================================================
Generating an EC private key
writing new private key to './sm2Certs/CE.key.pem'
-----
req: Skipping unknown attribute "/skip"
Signature ok
subject=C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = client enc (SM2)
Getting CA Private Key
Certificate:Data:Version: 3 (0x2)Serial Number:bd:61:fb:da:53:9a:1c:3cSignature Algorithm: sm2sign-with-sm3Issuer: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)ValidityNot Before: Nov 28 09:48:17 2022 GMTNot After : Jan 6 09:48:17 2027 GMTSubject: C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = client enc (SM2)Subject Public Key Info:Public Key Algorithm: id-ecPublicKeyPublic-Key: (256 bit)pub:04:c2:20:82:71:7b:46:8d:bf:98:df:1b:5f:51:28:40:96:cd:51:83:47:85:47:d0:da:b2:48:24:0e:0e:c7:28:29:9d:e0:14:15:e4:b9:2f:0d:2c:32:bc:54:dc:31:83:3c:5a:37:1a:1e:18:3e:0c:ba:9f:ec:70:9d:13:46:11:e5ASN1 OID: sm2p256v1NIST CURVE: SM2X509v3 extensions:X509v3 Basic Constraints: CA:FALSEX509v3 Key Usage: Key Encipherment, Data Encipherment, Key AgreementSignature Algorithm: sm2sign-with-sm330:44:02:20:6e:5b:c2:af:f3:65:eb:46:b1:01:76:2c:9c:ce:bc:22:55:da:94:af:31:a0:ef:eb:da:fa:1e:70:05:7f:91:b7:02:20:7d:3d:42:5e:40:b5:4d:7a:5c:0b:90:9d:40:6a:07:0d:45:bc:db:1a:49:50:b2:ed:3c:d6:71:91:a8:11:45:bc
-----BEGIN CERTIFICATE-----
MIICGTCCAcCgAwIBAgIJAL1h+9pTmhw8MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGFMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDEJTUkMgb2YgVEFTUzEZMBcGA1UEAwwQY2xpZW50IGVuYyAoU00y
KTBZMBMGByqGSM49AgEGCCqBHM9VAYItA0IABMIggnF7Ro2/mN8bX1EoQJbNUYNH
hUfQ2rJIJA4OxygpneAUFeS5Lw0sMrxU3DGDPFo3Gh4YPgy6n+xwnRNGEeWjGjAY
MAkGA1UdEwQCMAAwCwYDVR0PBAQDAgM4MAoGCCqBHM9VAYN1A0cAMEQCIG5bwq/z
ZetGsQF2LJzOvCJV2pSvMaDv69r6HnAFf5G3AiB9PUJeQLVNelwLkJ1AagcNRbzb
GklQsu081nGRqBFFvA==
-----END CERTIFICATE-----
chy-cpabe@ubuntu:~/double_certificate/test_sh$ ls
openssl.cnf SM2certGen.sh sm2Certs SM2.pem
chy-cpabe@ubuntu:~/double_certificate/test_sh$ cd sm2Certs/
chy-cpabe@ubuntu:~/double_certificate/test_sh/sm2Certs$ ls
CA.cert.pem CA.pem CE.key.pem CS.cert.pem CS.pem SE.key.pem SS.cert.pem SS.pem
CA.key.pem CE.cert.pem CE.pem CS.key.pem SE.cert.pem SE.pem SS.key.pem
chy-cpabe@ubuntu:~/double_certificate/test_sh/sm2Certs$ ll
总用量 68
drwxrwxr-x 2 chy-cpabe chy-cpabe 4096 11月 28 01:48 ./
drwxrwxr-x 3 chy-cpabe chy-cpabe 4096 11月 28 01:48 ../
-rw-rw-r-- 1 chy-cpabe chy-cpabe 875 11月 28 01:48 CA.cert.pem
-rw------- 1 chy-cpabe chy-cpabe 241 11月 28 01:48 CA.key.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 1335 11月 28 01:48 CA.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 790 11月 28 01:48 CE.cert.pem
-rw------- 1 chy-cpabe chy-cpabe 241 11月 28 01:48 CE.key.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 1253 11月 28 01:48 CE.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 794 11月 28 01:48 CS.cert.pem
-rw------- 1 chy-cpabe chy-cpabe 241 11月 28 01:48 CS.key.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 1258 11月 28 01:48 CS.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 790 11月 28 01:48 SE.cert.pem
-rw------- 1 chy-cpabe chy-cpabe 241 11月 28 01:48 SE.key.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 1253 11月 28 01:48 SE.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 790 11月 28 01:48 SS.cert.pem
-rw------- 1 chy-cpabe chy-cpabe 241 11月 28 01:48 SS.key.pem
-rw-rw-r-- 1 chy-cpabe chy-cpabe 1254 11月 28 01:48 SS.pem
chy-cpabe@ubuntu:~/double_certificate/test_sh/sm2Certs$
双向认证测试
服务端
- gmssl s_server -gmtls -accept 44330 -key SS.key.pem -cert SS.cert.pem -dkey SE.key.pem -dcert SE.cert.pem -CAfile CA.cert.pem -state -verify 1
chy-cpabe@ubuntu:~/double_certificate/test_sh/sm2Certs$ gmssl s_server -gmtls -accept 44330 -key SS.key.pem -cert SS.cert.pem -dkey SE.key.pem -dcert SE.cert.pem -CAfile CA.cert.pem -state -verify 1
verify depth is 1
Using default temp DH parameters
[GMTLS_DEBUG] set sm2 signing certificate
[GMTLS_DEBUG] set sm2 signing private key
[GMTLS_DEBUG] set sm2 encryption certificate
[GMTLS_DEBUG] set sm2 decryption private key
ACCEPT
SSL_accept:before SSL initialization
SSL_accept:before SSL initialization
SSL_accept:SSLv3/TLS read client hello
SSL_accept:SSLv3/TLS write server hello
SSL_accept:SSLv3/TLS write certificate
SSL_accept:SSLv3/TLS write key exchange
SSL_accept:SSLv3/TLS write certificate request
SSL_accept:SSLv3/TLS write server done
SSL_accept:SSLv3/TLS write server done
depth=1 C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)
verify return:1
depth=0 C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = client sign (SM2)
verify return:1
SSL_accept:SSLv3/TLS read client certificate
ssl_get_algorithm2=1734000008x
SSL_accept:SSLv3/TLS read client key exchange
SSL_accept:SSLv3/TLS read certificate verify
SSL_accept:SSLv3/TLS read change cipher spec
SSL_accept:SSLv3/TLS read finished
SSL_accept:SSLv3/TLS write change cipher spec
SSL_accept:SSLv3/TLS write finished
-----BEGIN SSL SESSION PARAMETERS-----
MIICmQIBAQICAQEEAuATBCB1GdDftz8QjZAogqTty/vAmqgraUSYwUlUYKBeLn4I
UwQwmpFOFPw9d7/GxkX1oXjNkvu15V9G3/tUwup5mENRZdqxCLUFpF0YpU0GDtfZ
fJddoQYCBGOEhsCiBAICHCCjggIgMIICHDCCAcGgAwIBAgIJAL1h+9pTmhw7MAoG
CCqBHM9VAYN1MIGCMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDFNPUkIgb2YgVEFTUzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAe
Fw0yMjExMjgwOTQ4MTdaFw0yNzAxMDYwOTQ4MTdaMIGGMQswCQYDVQQGEwJDTjEL
MAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcg
Sk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDEJTUkMgb2YgVEFTUzEaMBgG
A1UEAwwRY2xpZW50IHNpZ24gKFNNMikwWTATBgcqhkjOPQIBBggqgRzPVQGCLQNC
AATUszDy6KdmQt6kL7lcUVGmNavzAN/6bHy+is2HBwlfs3cY5pTGMuWn9sqtuba/
WwQY1aLWiAPopxBI9YuBgW+ioxowGDAJBgNVHRMEAjAAMAsGA1UdDwQEAwIGwDAK
BggqgRzPVQGDdQNJADBGAiEAnFE4yLsNb58hOeH+kZzj7F0jYq6rJj2+vMUuAyEz
VAoCIQDZZ6pVl+6Pu3z6MVq/9Qgf8r8PLMiIkA7olWVekws1E6QGBAQBAAAA
-----END SSL SESSION PARAMETERS-----
Client certificate
-----BEGIN CERTIFICATE-----
MIICHDCCAcGgAwIBAgIJAL1h+9pTmhw7MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGGMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDEJTUkMgb2YgVEFTUzEaMBgGA1UEAwwRY2xpZW50IHNpZ24gKFNN
MikwWTATBgcqhkjOPQIBBggqgRzPVQGCLQNCAATUszDy6KdmQt6kL7lcUVGmNavz
AN/6bHy+is2HBwlfs3cY5pTGMuWn9sqtuba/WwQY1aLWiAPopxBI9YuBgW+ioxow
GDAJBgNVHRMEAjAAMAsGA1UdDwQEAwIGwDAKBggqgRzPVQGDdQNJADBGAiEAnFE4
yLsNb58hOeH+kZzj7F0jYq6rJj2+vMUuAyEzVAoCIQDZZ6pVl+6Pu3z6MVq/9Qgf
8r8PLMiIkA7olWVekws1Ew==
-----END CERTIFICATE-----
subject=/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=client sign (SM2)
issuer=/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)
Shared ciphers:SM9-WITH-SMS4-SM3:SM9DHE-WITH-SMS4-SM3:SM2-WITH-SMS4-SM3:SM2DHE-WITH-SMS4-SM3:RSA-WITH-SMS4-SHA1:RSA-WITH-SMS4-SM3
CIPHER is SM2-WITH-SMS4-SM3
Secure Renegotiation IS supported
客户端
- gmssl s_client -gmtls -connect localhost:44330 -key CS.key.pem -cert CS.cert.pem -dkey CE.key.pem -dcert CE.cert.pem -CAfile CA.cert.pem -state
chy-cpabe@ubuntu:~/double_certificate/test_sh/sm2Certs$ gmssl s_client -gmtls -connect localhost:44330 -key CS.key.pem -cert CS.cert.pem -dkey CE.key.pem -dcert CE.cert.pem -CAfile CA.cert.pem -state
[GMTLS_DEBUG] set sm2 signing certificate
[GMTLS_DEBUG] set sm2 signing private key
[GMTLS_DEBUG] set sm2 encryption certificate
[GMTLS_DEBUG] set sm2 decryption private key
CONNECTED(00000003)
SSL_connect:before SSL initialization
SSL_connect:SSLv3/TLS write client hello
SSL_connect:SSLv3/TLS write client hello
SSL_connect:SSLv3/TLS read server hello
depth=1 C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = SORB of TASS, CN = Test CA (SM2)
verify return:1
depth=0 C = CN, ST = BJ, L = HaiDian, O = Beijing JNTA Technology LTD., OU = BSRC of TASS, CN = server sign (SM2)
verify return:1
SSL_connect:SSLv3/TLS read server certificate
Z=818CE57807A4D23F1F25A32D1C15EF46980AB3481FED36987D5D5BFCCCFEB367
C=00021E3082021A308201C0A003020102020900BD61FBDA539A1C3A300A06082A811CCF55018375308182310B300906035504061302434E310B300906035504080C02424A3110300E06035504070C074861694469616E31253023060355040A0C1C4265696A696E67204A4E544120546563686E6F6C6F6779204C54442E31153013060355040B0C0C534F5242206F6620544153533116301406035504030C0D546573742043412028534D3229301E170D3232313132383039343831375A170D3237303130363039343831375A308185310B300906035504061302434E310B300906035504080C02424A3110300E06035504070C074861694469616E31253023060355040A0C1C4265696A696E67204A4E544120546563686E6F6C6F6779204C54442E31153013060355040B0C0C42535243206F6620544153533119301706035504030C1073657276657220656E632028534D32293059301306072A8648CE3D020106082A811CCF5501822D03420004BD4B589F9688A74D5FB209590D4FBBDD6272B0E84CA89866A31B23B9DBCEBC2DA21CBED6DD2D13BD53E66F443E4EB6E5AFBC8B839B256654DDE3F7DD20512997A31A301830090603551D1304023000300B0603551D0F040403020338300A06082A811CCF5501837503480030450221009A59A4582AFFD6A403B56822EC52445AAA499A1861065C4FEDDC2C2BB262F48E022029A60A8E700091441812B67DD9C7F96616D38B6CD48399C77D676DF69451B1A8
SSL_connect:SSLv3/TLS read server key exchange
SSL_connect:SSLv3/TLS read server certificate request
SSL_connect:SSLv3/TLS read server done
SSL_connect:SSLv3/TLS write client certificate
SSL_connect:SSLv3/TLS write client key exchange
ssl_get_algorithm2=a512200008x
SSL_connect:SSLv3/TLS write certificate verify
SSL_connect:SSLv3/TLS write change cipher spec
SSL_connect:SSLv3/TLS write finished
SSL_connect:SSLv3/TLS write finished
SSL_connect:SSLv3/TLS read change cipher spec
SSL_connect:SSLv3/TLS read finished
---
Certificate chain0 s:/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=server sign (SM2)i:/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)1 s:/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=server enc (SM2)i:/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)2 s:/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)i:/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)
---
Server certificate
-----BEGIN CERTIFICATE-----
MIICGzCCAcGgAwIBAgIJAL1h+9pTmhw5MAoGCCqBHM9VAYN1MIGCMQswCQYDVQQG
EwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcMB0hhaURpYW4xJTAjBgNVBAoMHEJl
aWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4xFTATBgNVBAsMDFNPUkIgb2YgVEFT
UzEWMBQGA1UEAwwNVGVzdCBDQSAoU00yKTAeFw0yMjExMjgwOTQ4MTdaFw0yNzAx
MDYwOTQ4MTdaMIGGMQswCQYDVQQGEwJDTjELMAkGA1UECAwCQkoxEDAOBgNVBAcM
B0hhaURpYW4xJTAjBgNVBAoMHEJlaWppbmcgSk5UQSBUZWNobm9sb2d5IExURC4x
FTATBgNVBAsMDEJTUkMgb2YgVEFTUzEaMBgGA1UEAwwRc2VydmVyIHNpZ24gKFNN
MikwWTATBgcqhkjOPQIBBggqgRzPVQGCLQNCAASBCQ3s0ZmPDShfvYPhLAGvu/W8
UJsw7PHGOUzA31Bu/G2ORzpzvywqKdrc0Y3h/IYfR50wzwtATIKZ9kXJi2rqoxow
GDAJBgNVHRMEAjAAMAsGA1UdDwQEAwIGwDAKBggqgRzPVQGDdQNIADBFAiEA57xI
qOPxZ0hnvfII5z3G5SpgLmOsCCgJZQTarNaigVwCIDbMyT3lN2RSSd4nbfd2R3z3
im33yunP+7JtZu5CvED1
-----END CERTIFICATE-----
subject=/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=BSRC of TASS/CN=server sign (SM2)
issuer=/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)
---
Acceptable client certificate CA names
/C=CN/ST=BJ/L=HaiDian/O=Beijing JNTA Technology LTD./OU=SORB of TASS/CN=Test CA (SM2)
Client Certificate Types: RSA sign, DSA sign
---
SSL handshake has read 2121 bytes and written 2113 bytes
Verification: OK
---
New, GMTLSv1.1, Cipher is SM2-WITH-SMS4-SM3
Server public key is 256 bit
Secure Renegotiation IS NOT supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
SSL-Session:Protocol : GMTLSv1.1Cipher : SM2-WITH-SMS4-SM3Session-ID: 7519D0DFB73F108D902882A4EDCBFBC09AA82B694498C1495460A05E2E7E0853Session-ID-ctx: Master-Key: 9A914E14FC3D77BFC6C645F5A178CD92FBB5E55F46DFFB54C2EA7998435165DAB108B505A45D18A54D060ED7D97C975DPSK identity: NonePSK identity hint: NoneSRP username: NoneStart Time: 1669629632Timeout : 7200 (sec)Verify return code: 0 (ok)Extended master secret: no
---
参考链接
- 基于openssl和国密算法生成CA、服务器和客户端证书_MY CUP OF TEA的博客-CSDN博客_openssl生成国密证书
- gmssl服务端和客户端程序、吉大正元身份认证网关、吉大正元SDK+USBkey 两两之间双证书双向认证数据通信测试_MY CUP OF TEA的博客-CSDN博客_身份认证网关客户端服务